Practical Guide to Trusted Computing , A (IBM Press) 1, Challener, David, Yoder, Kent, Catherman, Ryan, Safford, David, Van Doorn, Leendert, Yoder, Kent, Catherman, Ryan, Safford, David, Van Doorn, Leendert, eBook - Amazon.com
D3.9: Study on the Impact of Trusted Computing on Identity and Identity Management: Future of IDentity in the Information Society




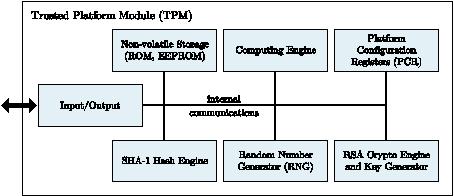
![PDF] Trusted Computing Platforms , the Next Security Solution | Semantic Scholar PDF] Trusted Computing Platforms , the Next Security Solution | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/4a82f9c66e39b1335bdc8fa3eb0880e9a0370446/9-Figure2-1.png)